
Lionakis Accelerates Projects and Prevents Disruption with Egnyte
Lionakis Accelerates projects and Prevents Disruption With Egnyte
Read →
Lionakis Accelerates projects and Prevents Disruption With Egnyte
Read →
Harness the Power of Data to Transform Traditional Practices Most AEC professionals rely on years of experience and instinct. The advent of a centralized, cloud platform has led to a paradigm shift, with data now driving decisions. Egnyte’s Beyond Blueprints Ebook outlines how to embrace the change and harness the power of data for:• Secure […]
Read →
This report from IDC research highlights the return-on-investment achieved by global CyberArk customers. The report calculates the risk reduction, cost savings, and productivity benefits real-world organizations have achieved in their hybrid and multi-cloud environments with the CyberArk Identity Security Platform.
Read →
Outpacing the adversary The Trend 2025 Cyber Risk Report sustains our shift towards proactive security. Protecting enterprises is no longer about stopping breaches but is now about staying ahead, making cybersecurity a business enabler. This report looks at our telemetry from 2024: by looking at last year’s risk landscape, we recognize exposures and understand attacker […]
Read →
In an increasingly complex cyber threat landscape, organizations need more than static assessments—they require continuous, quantifiable visibility into their cyber risk. This technical report introduces and explains Trend Micro’s Cyber Risk Exposure Management (CREM) and its core output: the Cyber Risk Index. The Cyber Risk Index provides a dynamic and real-time measurement of organizational cyber […]
Read →
Proactively uncover, predict, assess, and mitigate cyber risks – prioritizing impact, reducing exposure, and building cyber resilience.
Read →
The data breach. A never-ending thorn in the side of many CISOs, CIOs and other cybersecurity professionals. Sometimes it feels like despite all organizations do to prevent them, some new issue pops up every year that we have to solve for. But throwing in the towel simply isn’t an option. Especially as one of the […]
Read →
Accelerate 2025: Financial Services Virtual Conference With the right data, technology, and access, any financial organization can improve its business-critical workflows. Accelerate is Snowflake’s largest financial services virtual event, where technology leaders share industry trends and how their organizations are accelerating with AI and data strategies. In this on-demand virtual conference, you’ll learn from data […]
Read →
A well-defined code signing policy helps protect software, streamline security practices, and enable developers to follow best practices with confidence. This guide walks you through creating an effective policy, covering key concepts, policy development steps, and practical implementation strategies to strengthen security without disrupting workflows. Whether you’re formalizing a new policy or refining an existing […]
Read →
Building security into your software release process doesn’t have to slow you down. The right code signing solution helps you protect authenticity, reduce vulnerabilities, and maintain compliance—all while keeping development efficient. This guide walks you through what to look for in a platform, from secure key management and automation to flexible configuration and enterprise-wide visibility.
Read →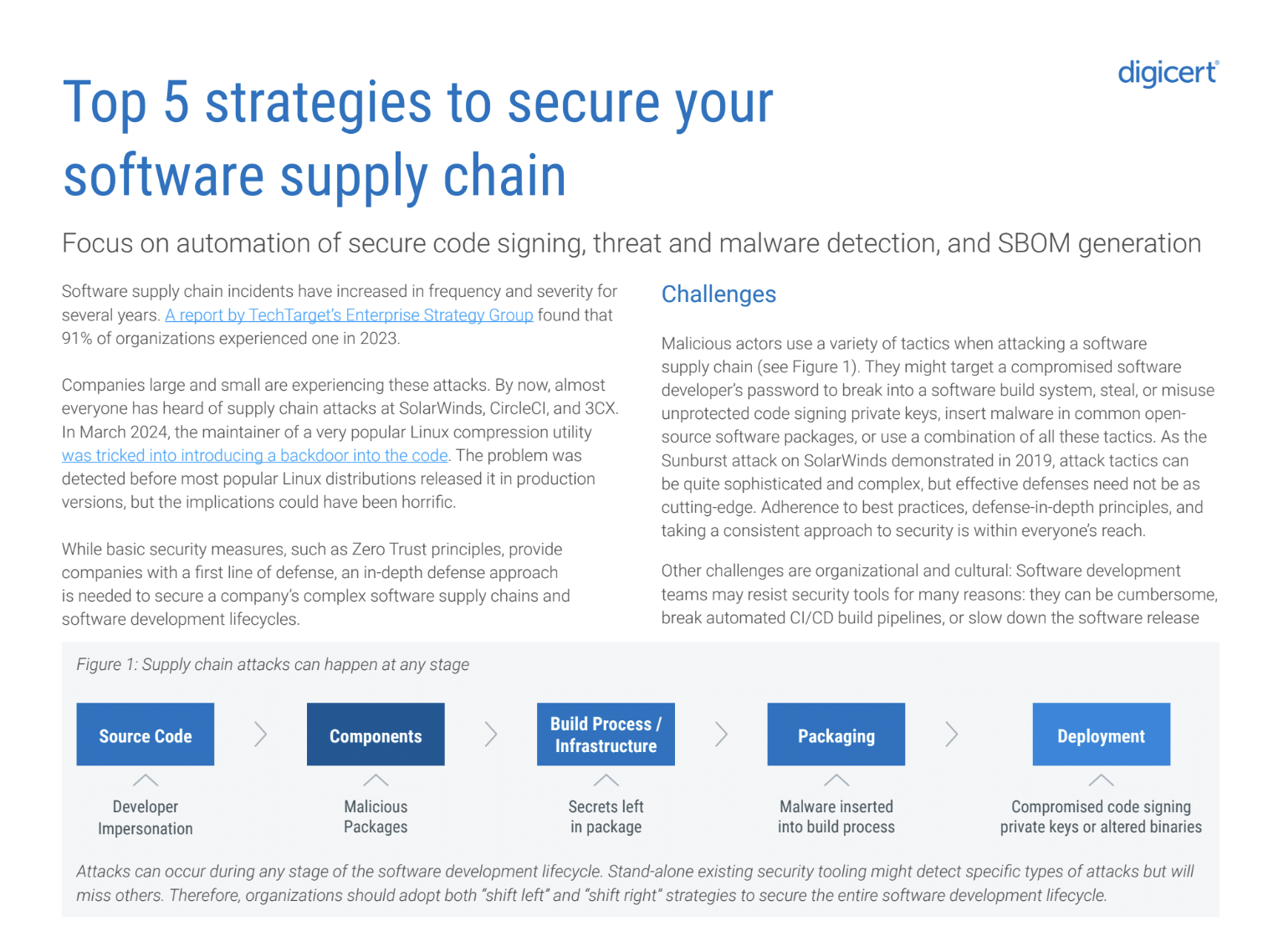
Software supply chain attacks are growing in frequency and sophistication, targeting organizations of all sizes. Even strong single solutions like Zero Trust leave gaps in your full DevOps cycle. From automation to compliance tools and policies, these 5 strategies will mitigate risks at every stage of your software development. Download the guide now.
Read →
This editable sample code signing policy provides a ready-to-use framework based on industry best practices. Use it as-is or tailor it to fit your organization’s needs, ensuring secure code signing within your CI/CD pipeline. The right tools exist to protect software, but they’re only effective when used correctly. A strong code signing policy ensures that […]
Read →