
Lionakis Accelerates Projects and Prevents Disruption with Egnyte
Lionakis Accelerates projects and Prevents Disruption With Egnyte
Read →
Lionakis Accelerates projects and Prevents Disruption With Egnyte
Read →
Harness the Power of Data to Transform Traditional Practices Most AEC professionals rely on years of experience and instinct. The advent of a centralized, cloud platform has led to a paradigm shift, with data now driving decisions. Egnyte’s Beyond Blueprints Ebook outlines how to embrace the change and harness the power of data for:• Secure […]
Read →
In Forrester’s 36-criteria evaluation of distributed denial of service providers, nine of the most significant companies were identified in a crowded field of competitors. These companies were researched, analyzed, and scored to determine which are best able to safeguard their customer’s business. Read this report to learn about how the industry leaders are mitigating these […]
Read →
This research was conducted to understand how organizations are protecting web applications, and how web application attacks affect both an organization’s security posture and bottom line. Ponemon Institute surveyed 594 individuals familiar with the Open Web Application Security Project (OWASP), and organization responsible for increasing awareness of and highlighting risks to web applications. Read this […]
Read →
Online shoppers are browsing and buying more frequently than ever before, and they are doing so from multiple networks, locations, and mobile devices across the globe. This report highlights the opportunities mobile commerce presents, as well as the importance of and challenges associated with ensuring optimal performance for mobile commerce experiences. It also highlights approaches […]
Read →
This research was conducted to understand the cost and consequences of these security threats. Ponemon Institute surveyed 641 individuals involved in preventing, detecting, and containing denial-of-service attacks against their organizations. Most participants in this research work in IT operations, IT security, IT compliance, or data center administration. Read this report to learn more about the […]
Read →
The Importance of Improving and Adapting Web Security With so much depending on website availability, CSOs are considering new, cost-effective ways to be proactive and vigilant. Understand the challenges to web security deployments.
Read →
How do you choose the best cloud security solution? In today’s faster forward world, denial of service, data breaches, and SQL injection attacks are growing faster than on-premises firewalls can scale – you need a cloud-based security solution to meet the threat. Learn about the various solutions and techniques for web, DNS, and infrastructure security.
Read →
How to Choose a Web Application Firewall (WAF) – Use these seven questions as criteria to choose the right Web Application Firewall for your website or web application.
Read →
The global increase in DDoS attacks has sparked an increased demand for mitigation services. In response, a number of new DDoS mitigation service providers have entered the marketplace. For enterprises seeking protection, assessing and differentiating between DDoS mitigation providers can be difficult, especially because many of these services reside in the cloud. This Akamai white […]
Read →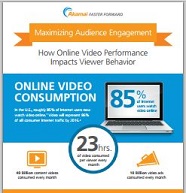
Speed matters when it comes to online video viewing by today’s content hungry consumers. Anything over a 2 second delay causes viewer abandonment and losses to the bottom line. Find all the compelling statistics about the lasting effect of online video failure here.
Read →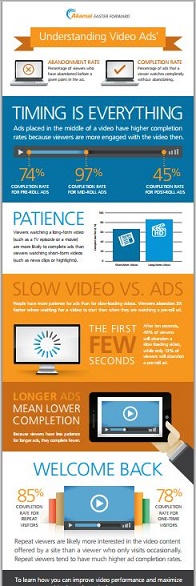
This infographic explains how timing and the type of video content being viewed influence the completion rate of Ads. Learn everything you need to know about ad placement, and when slow video or the length of Ads matter.
Read →